Cyber threats are becoming more severe with the widespread use of remote technologies and the increasing sophistication of attacks. Recent analyses indicate that attackers are exploiting vulnerabilities at unprecedented speeds. In 2023, the average time to exploit a vulnerability after public disclosure decreased to just five days, a significant reduction from 32 days in 2022. Notably, 12% of these vulnerabilities were exploited within a day, 29% within a week, and 56% within a month. This trend underscores the critical need for organizations to implement rapid patching and robust security measures to mitigate the heightened risk of swift exploitation.
“It’s not just an arms race between adversaries and defenders in terms of conducting cyberattacks and protecting against them. There’s a sprint taking place as well in detecting systems with known vulnerabilities to cyberthreats,” the report says.
Threat intelligence is no longer a luxury. The evolving landscape requires that threat analysts develop a consistent process to monitor new attack types and compare them to an organization’s security capabilities. By understanding who is targeting your industry and their methods, you can prioritize appropriate countermeasures. Threat intelligence is only valuable if you apply insights about how attackers are targeting organizations to anticipate how they might target your own environment.
Bridging the gap between threat intelligence and your controls is where many organizations struggle. Advanced threat intelligence platforms can automate the mapping of threat actors to indicators of compromise (IoCs), but this analysis can also be performed without expensive tools.
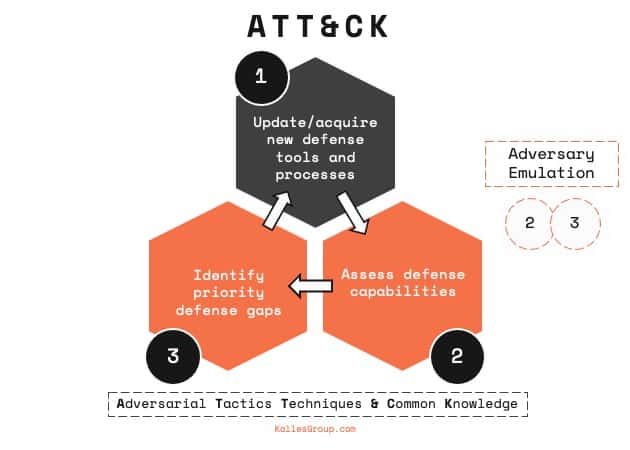
As the industry’s standard for organizing knowledge about cyber adversary behaviors, the MITRE ATT&CK framework helps facilitate comprehensive internal and external incident analysis. MITRE ATT&CK framework explained: it is a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. By utilizing MITRE ATT&CK, threat intelligence professionals can move away from indicator-driven defense models that often distort objectives and hinder response times. With MITRE ATT&CK, security leaders can make strategic decisions that enhance the effectiveness of their security investments. However, the framework is complex and may need to be tailored to fit each organization’s needs.
This article answers the following questions:
- What is the MITRE ATT&CK framework?
- What other model can help prevent and preempt cyber attacks?
- How can the MITRE ATT&CK framework and other models be adapted to best suit an organization’s needs?
What is the MITRE ATT&CK framework?
MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. The ATT&CK knowledge base is used as a foundation for developing specific threat models and methodologies in the private sector, government, and cybersecurity community.
MITRE ATT&CK provides details on many threat actors and groups, including which techniques and tools they typically use, based on open-source reporting. The framework was introduced in 2013, funded by the National Institute of Standards and Technology (NIST).
Initially, the framework focused on post-compromise detection, or an attacker’s behavior after gaining access to a network. To address pre-compromise activities, MITRE added two new tactics in October 2020: Reconnaissance and Resource Development.
This expansion underscores the framework’s adaptability in addressing modern threats. Understanding how adversaries operate is key to staying ahead of cyber threats. Learn more about navigating today’s complex threat landscape and how frameworks like MITRE ATT&CK play a pivotal role in shaping proactive defense strategies in our post, Security Success: Navigating the Threat Landscape.
The current structure of MITRE ATT&CK
The MITRE ATT&CK framework includes the following components:
- Tactics and Techniques (“TT”): A way of looking at cyberattacks beyond the results of the attack. Tactics are the adversary’s goals or reasons behind an attack. Techniques are the methods adversaries use to achieve their objectives. Tactics and techniques help analysts view an attack in progress as well as indicators of compromise (IoCs).
- Common Knowledge (“CK”): Documented use of tactics and techniques—an archive of procedures, commonly referred to as Tactics, Techniques, and Procedures (TTPs).
MITRE divides ATT&CK into several matrices, each containing various tactics and techniques associated with their subject matter. For example, Enterprise ATT&CK contains tactics and techniques that apply to Windows, Linux, and macOS systems, while Mobile ATT&CK contains tactics and techniques relevant to mobile devices.
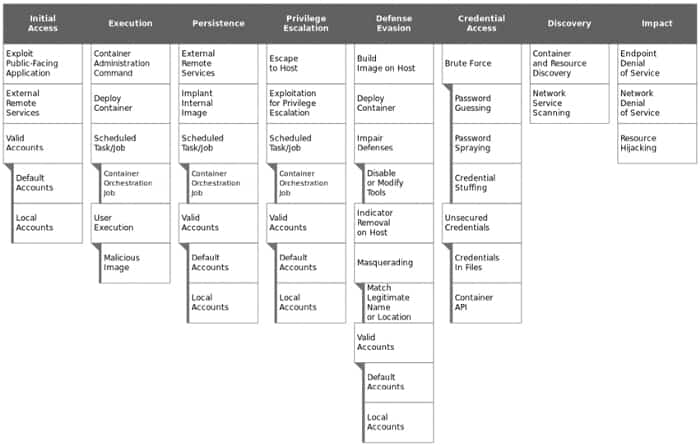
Since the framework contains a comprehensive representation of adversary behaviors when compromising networks, it’s useful for various offensive and defensive strategies.
Why use MITRE ATT&CK?
MITRE ATT&CK helps organizations truly understand adversaries and how they operate. ATT&CK maps every attack phase against specific methods that attackers use to carry out attacks. Organizations need to look at what they are trying to protect, how those resources might be attacked, and what adversaries are targeting to determine which attack phases to focus on.
For instance, if a company is at high risk of being targeted by ransomware groups, the company can use the MITRE ATT&CK framework to see how these groups may deploy their attacks. Viewing the entire attack chain provides insight into how a ransomware attacker would move through your network, which helps an organization focus its defense, monitoring, and detection efforts.
The framework can also be used for adversary emulation and Red Teaming. Defenders can simulate common adversary behavior to find gaps in visibility, defensive tools, and processes.
Questions that MITRE ATT&CK can help answer include:
- How effective are my defenses?
- Given limited resources, where should we prioritize spending?
- Can I detect a known adversary?
- Is the data that we collect useful?
- How can we evaluate our security tools?
Challenges with MITRE ATT&CK
While MITRE ATT&CK offers many benefits, the framework is extensive and can be complex due to its detailed nature. There are over 100 different attack patterns. Mapping a company’s security infrastructure from scratch can be daunting and time-consuming. Additionally, the framework may not fully address insider threats, which are increasingly a concern. For these reasons, defenders should be aware of other models, such as the Cyber Kill Chain.
What other framework can help prevent and preempt cyber attacks?
The Cyber Kill Chain model
Another popular framework that helps analyze and prevent cyber attacks is the Cyber Kill Chain model. Developed by Lockheed Martin, the Cyber Kill Chain applies the concept of the military kill chain to cyber attacks. It’s designed for defenders to improve their security by analyzing an attacker’s methodology and interrupting the attack at each phase.
However, some critics of the model as a threat assessment and prevention tool point out:
- The initial phases happen outside of the defended network, making it difficult to identify or defend against actions in these phases.
- The methodology is outdated because it reinforces traditional perimeter-based and malware-prevention defensive strategies.
- It does not model insider threats well, which is problematic because many attackers begin by using valid account credentials to access the network—activity that might not be detected as malicious.
Cyber Kill Chain vs MITRE ATT&CK
Comparing the Cyber Kill Chain vs MITRE ATT&CK, both frameworks aim to understand and stop cyber attacks but differ in scope and application. The Cyber Kill Chain provides a linear sequence of stages that an external attacker follows, while MITRE ATT&CK offers a more detailed matrix of tactics and techniques used by adversaries, including both external and insider threats.
Organizations may benefit from combining insights from both frameworks to enhance their risk threat assessment. By understanding the strengths and limitations of each model, security teams can develop more robust defense strategies.
How can the MITRE ATT&CK framework and other models be adapted to best suit an organization’s needs?
To address the limitations of the traditional kill chain and the internal focus of the MITRE ATT&CK framework, a unified version was developed in 2017 by Paul Pols in collaboration with Fox-IT and Leiden University.
Uniting the frameworks: The Unified Kill Chain
The Unified Kill Chain provides a linear arrangement of 18 unique attack phases that may occur in end-to-end cyber attacks, covering activities that could occur both outside and within a network.
With growing trends of ransomware-as-a-service and attacks against critical infrastructure, organizations can use the Unified Kill Chain to understand how adversaries may progress through an attack. This unified model incorporates elements from both the MITRE ATT&CK framework and the Cyber Kill Chain, providing a comprehensive view.
The three focuses of the Unified Kill Chain include:
- Initial Foothold
- Network Propagation
- Action on Objectives

Regardless of which framework an organization chooses, setting up a repeatable process for monitoring which types of attacks are happening internally and in the larger industry can significantly reduce the impact of future attacks.
By adapting the MITRE ATT&CK framework explained here, the Cyber Kill Chain model, or similar frameworks, organizations can skillfully inform management’s decision-making processes, enhance engineering efforts, create an overview of the company’s security posture, and proactively protect the organization from future cyber attacks, including insider threats.
Additional considerations for using MITRE ATT&CK in risk threat assessment
- MITRE ATT&CK insider threat: Incorporate techniques related to insider threats into your assessment to address risks from within the organization.
- Risk threat assessment MITRE ATT&CK: Use the framework to perform thorough risk assessments by mapping potential threats to specific tactics and techniques.
Conclusion
In a rapidly changing cyber landscape, understanding and utilizing frameworks like MITRE ATT&CK is essential. By comparing models like the Cyber Kill Chain vs MITRE ATT&CK, organizations can choose or adapt a framework that best suits their needs. Implementing these frameworks effectively requires effort but can greatly enhance an organization’s ability to defend against cyber threats.
