From Tool to Teammate: Smart Cookies Recap on Leading with AI
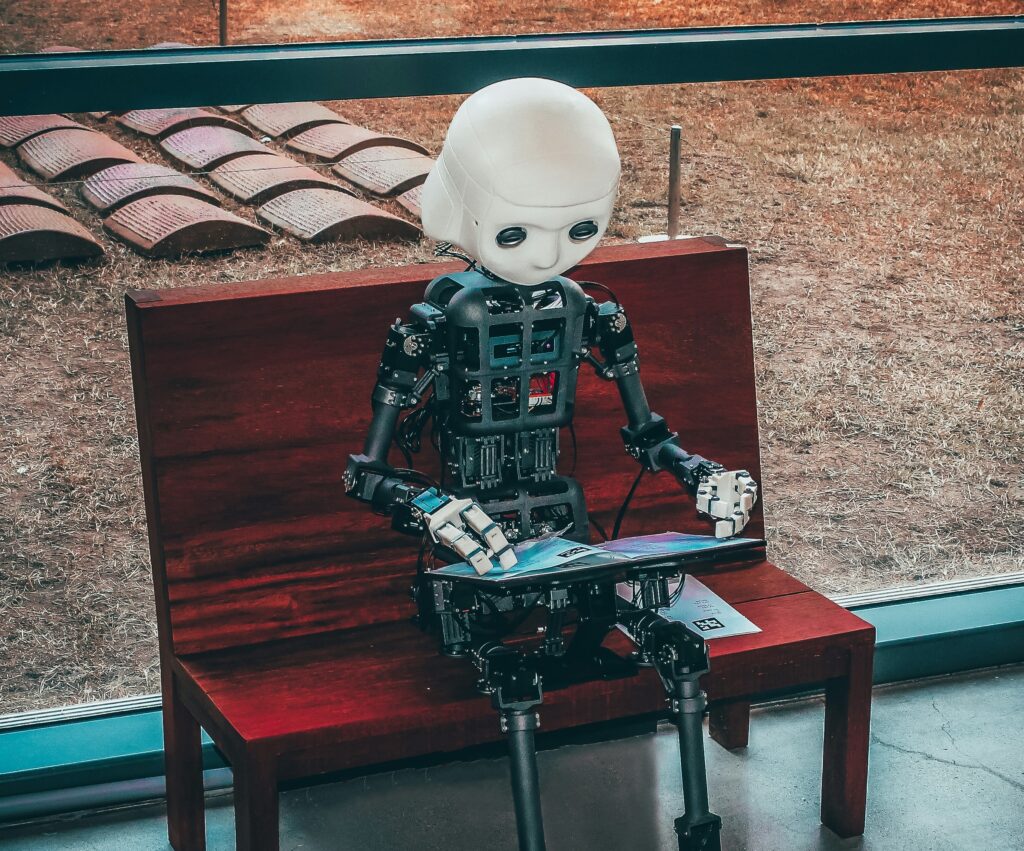
What happens when AI stops being a novelty, and starts shaping how teams actually work? That’s the question we unpacked at our latest Smart Cookies event, where a room full of leaders gathered to explore how AI moves from curiosity to capability, and eventually, from sidekick to system. Our evening was hosted by Bryon Scharenberg […]
From Tool to Teammate: Smart Cookies Recap on Leading with AI Read More »